UK’S TECH SUCCESS ARCHITECTS
The Architecture of
Resilience.
Powered by IBM, Managed by Syscomm.
When ransomware is inevitable, recovery must be instant. Meet the new FlashSystem.ai, the intelligent guardian that turns your storage into an active administrator.
- Over 200 successful incident recoveries managed since 1984
- Since 1984
Four Decades of Eliminating Technology Gaps.
Syscomm has evolved alongside the world’s most demanding IT environments. We are technical architects who have navigated 200+ successful ransomware recoveries.
As a trusted UK ISP and IT Infrastructure Architect, we understand that: When the cumulative probability of a cyber attack reaches 95% over three years, it stops being a risk. It becomes a certainty.
"When odds reach 95%, they stop being a probability. They become a certainty."
Introducing A Solution Beyond Backup
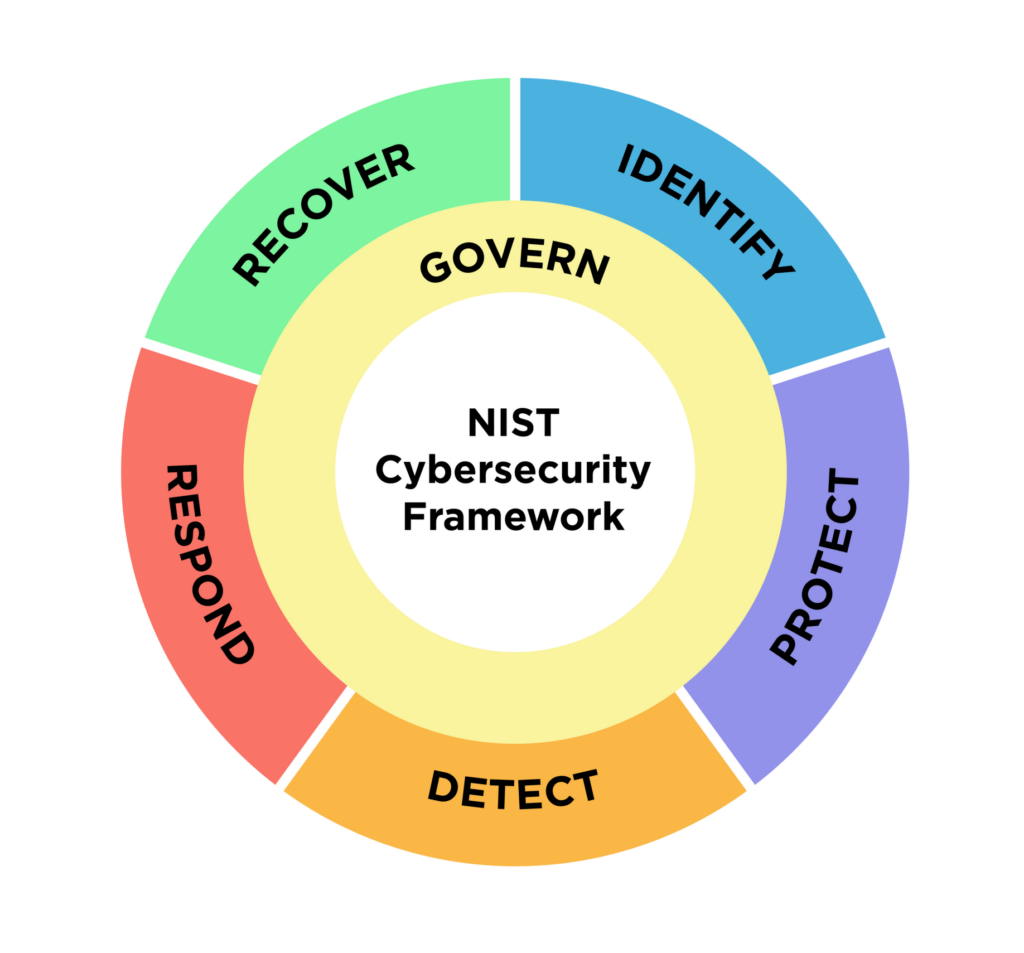
Why Storage Is The New Frontier
Most security strategies focus heavily on the perimeter—building higher walls to keep attackers out. But in the modern threat landscape, the perimeter is no longer enough. When attackers inevitably breach the walls, they target your backups first in 94% of cases to force a payout.
Syscomm recommends a shift in architecture that moves resilience from “outside the box” to inside the hardware. It is the only foundation that can guarantee a clear path to recovery when every other layer of your security stack has been compromised.
Data Layer Resilience
It embeds cyber-resilience directly into the data layer, creating an "air-gapped" recovery environment inside your storage.
The Backup Trap
Ransomware now targets backup servers first. You need a recovery point that doesn't depend on "hoping the backups are okay".
The Recovery Gap
You face a 76-day average recovery window. Without storage-native resilience, a breach isn't an incident—it’s a business-ending event.
Your AI Co-Administrator Never Sleeps
It’s not just storage. It’s agentic AI embedded directly into your storage – acting in real time to prevent disaster.
90% Less Manual Management
Autonomous tuning and optimisation reduce human touchpoints and potential configuration mistakes.
Autonomous tuning
Predictive health analysis
Fewer human errors.
Ransomware Detection in 60 secs
Detection happens at the flash drive level. Every I/O is analysed in real time with zero performance penalty.
Drive-level analysis
Real-time I/O monitoring
No latency impact.
50% Faster Compliance
Automated evidence collection and continuous compliance posture checks built for regulated industries.
Automated evidence
Continuous posture check
Regulatory ready.
This isn’t monitoring. It’s intervention.
Built For The Moment When Everything Goes Wrong
Four FlashSystem capabilities engineered for when it matters the most. Architected into your environment by Syscomm, so they actually work when you need them.
Protect
Protect
Detect
Detect
Recover
Recover
Future-Proof
Future-Proof
Capability Isn't Resilience. Architecture Is.
FlashSystem gives you the hardware. But in every ransomware recovery we’ve led, the difference between a clean restore and a business-ending event came down to one thing: how the platform was designed, configured, and tested before the incident.
That’s why every Syscomm FlashSystem deployment follows a 7-step resilience roadmap — from strategic assessment and Safeguarded Copy policy design, through deployment, to recovery validation against real-world attack scenarios. Capability becomes resilience only when it’s architected in.
"Recovery is rarely limited by technology, but by design and configuration."
We Don't Just Recommend IBM FlashSystem.
We Run Our Business On It.
Before we ever quoted FlashSystem to a client, Syscomm deployed it across all of our 6 UK data centres: retiring our SAS-based SAN in favour of NVMe-backed, AI-driven storage engineered for the threat landscape we deal with every day.
We’re a vendor-agnostic MSP. We evaluated Pure Storage, NetApp, HPE and IBM side by side. FlashSystem won on the criteria that actually matter when an incident hits: drive-level ransomware detection in under 60 seconds, immutable snapshots no compromised admin can delete, and dual-authorisation controls on every destructive action.
That infrastructure is live today, running production workloads for the businesses we protect.

Cyber Resilience Assessment
Your journey towards data resilience is a complex one and can be confusing for many organisations.
This short cyber resilience assessment is a first step towards achieving end-to-end resilience for your organisation.
- Takes less than 5 mins
- Receive a personalised readiness score
Ready to find your gaps?
Identify vulnerabilities in your current storage architecture and receive a roadmap for improvement.
Explore Our Configurations
The IBM FlashSystem product line is our chosen foundation for speed, density, and cyber-resilience. Find the right FlashSystem tailored to your storage needs
IBM FlashSystem 5600
- Data Reduction with no performance impact
- AI-driven dynamic storage
- In-line Threat Detection
- NVMe EDSFF
- 1U rack space, 12 drives
- 2×12 Core Intel Xeon
- PCle Gen 4
- 16x FC or 20x ethernet ports
- Max IOPs: 2.6 million
- Read BW: 30 GB/s
- Single System Storage Starting From 33TB to Max Capacity:
633 TB raw
400 TBu
2.4 PBe - 5th generation FCM
IBM FlashSystem 7600
- Data Reduction with no performance impact
- AI-driven dynamic storage
- In-line Threat Detection
- NVMe EDSFF
- 2U rack space, 32 drives
- 2×16 Core AMD Epyc
- PCle Gen 5
- 32x FC or ethernet ports
- Max IOPs: 4.3 million
- Read BW: 55 GB/s
- Single System Storage Starting From 80TB to Max Capacity:
1.68 PB raw
1.2 PBu
7.2 PBe - 5th generation FCM

IBM FlashSystem 9600
- Data Reduction with no performance impact
- AI-driven dynamic storage
- In-line Threat Detection
- NVMe EDSFF
- 2U rack space, 32 drives
- 2×48 Core AMD Epyc
- PCle Gen 5
- 32x FC or ethernet ports
- Max IOPs: 6.3 million
- Read BW: 86 GB/s
- Single System Storage Starting From 470TB to Max Capacity:
3.37 PB raw
2.4 PBu
11.8 PBe - 5th generation FCM

We Don't Just Sell IT. We Architect Security.

With over 40 years of experience, Syscomm builds cyber‑resilient environments that stand up under pressure, acting as your one‑stop technology architect to eliminate the gaps others leave open.
Gap Analysis
Deep dive into your current storage posture.
Recovery Time
Realistic audit of recovery time objectives.
Executive Report
Strategy-ready insights for your board.
- Managed End-to-End by Syscomm Success Architects
Upcoming Syscomm x IBM Event
27
th
April 2026

Defending Your Data – Cyber Safe Experience
Join us at IBM’s headquarters & discover new ways to defend your data.
Ready to elevate your storage strategy?
Modernise your storage with confidence. Whether you’re refreshing ageing infrastructure, addressing performance bottlenecks, or strengthening protection against ransomware, we’ll help you design an IBM FlashSystem solution aligned with your workloads, growth ambitions, and recovery objectives.
- Book your discovery session now