Storage Built for the Worst-Case Scenario.
We don’t just sell IBM FlashSystem; we architect the resilience your business demands. Bridge the recovery gap with an architecture-first approach to data protection.
Our Approach
Technology alone does not deliver resilience. Even the most advanced storage platforms will realise their full value when deployed within an architecture that understands how modern systems fail, how attackers operate, & how organisations must recover when incidents occur.
At Syscomm, we approach IBM FlashSystem deployments with this wider perspective. Our role is not simply to install a storage array, but to design a data platform that supports performance, availability, & cyber recovery as part of the organisation’s overall infrastructure strategy.
The "Backup Trap" & The "Recovery Gap"
Most storage deployments focus on “speeds and feeds.” But in an era of sophisticated ransomware, performance is secondary to survivability. The “Backup Trap” leads to a “Recovery Gap”—where data exists, but the infrastructure to restore it is compromised.
Through years of supporting organisations during ransomware incidents and major infrastructure failures, we have seen first-hand that recovery is rarely limited by the technology itself. More often, the challenge lies in how systems were designed, how protection policies were implemented, and whether recovery processes were properly considered before an incident occurred.
“Recovery is rarely limited by technology, but by design & configuration.”
The Problem
Legacy storage architectures treat backup as a separate silo, leaving primary data vulnerable to encryption and slow recovery times.
The Syscomm Solution
We architect storage as the new frontier of security, integrating immutable snapshots directly into the data layer for near-instant recovery.
The 7-Step Resilience Roadmap
Our consultative approach ensures your IBM FlashSystem deployment is optimized for performance, security, and long-term governance.
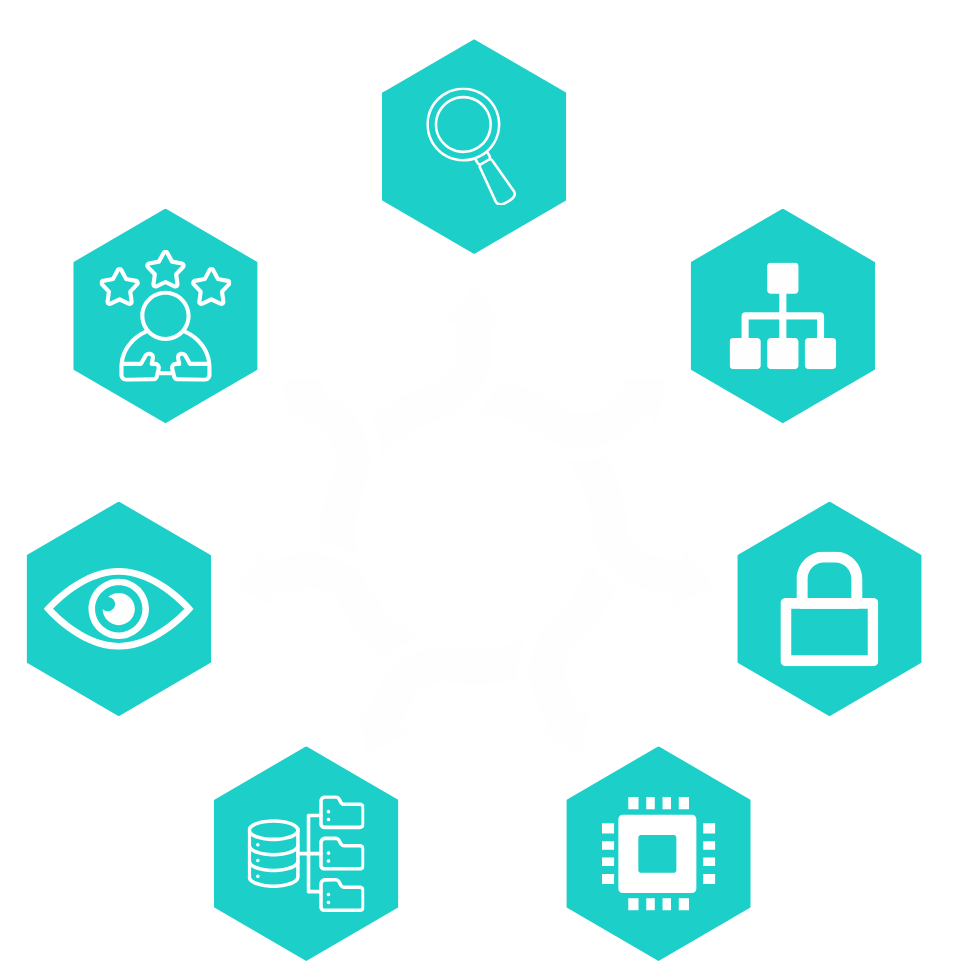
Step 1: Strategic Assessment
Strategic Assessment
Phase 01 of Implementation
Before any technology is deployed, Syscomm works with organisations to understand the operational, security, and resilience requirements that storage must support. Rather than simply replacing storage infrastructure, the objective is to determine how FlashSystem should sit within a wider resilience strategy.
- Key Deliverables
- Current data architecture and performance bottlenecks
- Existing backup and disaster recovery approach
- Ransomware resilience and recovery expectations
- Compliance or regulatory requirements
- Critical applications and recovery objectives (RPO/RTO)
Expert’s Note:
“This phase is critical for ensuring that the final architecture supports the organisation’s availability, performance, and cyber-recovery objectives.“
Step 2: Architecture Design
Architecture Design
Phase 02 of Implementation
Once requirements are understood, Syscomm designs a storage architecture that maximises the capabilities of IBM FlashSystem.
- Key Deliverables
- Storage tiering and workload placement
- Integration with virtualisation platforms (VMware, Hyper-V, Kubernetes)
- Storage networking design (SAN / NVMe / IP architectures)
- Snapshot and Safeguarded Copy strategy
- Integration with backup, replication, and DR platforms
Expert’s Note:
“This phase is critical for building an architecture that delivers high performance while embedding cyber resilience directly into the storage layer, to ensure the solution scales cleanly as data volumes grow.
Step 3: Cyber Resilience Planning
Cyber Resilience Planning
Phase 03 of Implementation
FlashSystem provides powerful ransomware protection features, but they must be correctly configured to deliver maximum protection. Implementing Safeguarded Copy and immutable snapshots. We ensure you always have a “clean” recovery point that ransomware cannot touch.
- Key Deliverables
- Snapshot frequency aligned to recovery objectives
- Secure administrative access controls
- Immutable Safeguarded Copy policies
- Air-Gapped Data Logic
Expert’s Note:
“This phase is critical for ensuring the storage platform becomes an active component of the organisation’s cyber defence strategy, not simply a data repository.“
Step 4: Deployment & Integration
Deployment & Integration
Phase 04 of Implementation
Seamlessly weaving IBM FlashSystem into your existing organisation’s environment, with minimal disruption to live operations.
- Key Deliverables
- Hardware Installation & Provisioning
- Integration with existing compute and hypervisors
- Executive Risk Assessment Report
- Migration of existing storage workloads
- Replication and DR configuration
- Performance optimisation
Expert’s Note:
“This phase is critical as careful migration planning ensures workloads are transitioned with minimal operational disruption.“
Step 5: Hosting & Private Infrastructure Options
Hosting & Private Infrastructure Options
Phase 05 of Implementation
For organisations seeking additional resilience or simplified operations, Syscomm can also deliver FlashSystem within a hosted or hybrid infrastructure model.
- Key Deliverables
- FlashSystem deployed within Syscomm data centres
- Private storage infrastructure delivered as a managed platform
- Replication between customer sites and Syscomm facilities
- Hybrid storage models combining on-premise and hosted environments
Expert’s Note:
“This approach allows organisations to benefit from enterprise storage capabilities without the operational overhead of running complex infrastructure internally.“
Step 6: Operational Visibility
Operational Visibility
Phase 06 of Implementation
Once deployed, Syscomm provides ongoing operational support and monitoring to ensure the platform continues to deliver performance and resilience.
- Key Deliverables
- Proactive system monitoring
- Performance optimisation
- Firmware and lifecycle management
- Capacity planning
- Integration with security monitoring platforms
Expert’s Note:
“This phase is critical for ensuring that the strategic assessment aligns with your long-term business continuity goals.”
Step 7: Experience That Matters
Experience That Matters
Phase 07 of Implementation
Syscomm brings extensive experience supporting organisations through major cyber incidents and data recovery scenarios..
- Key Deliverables
- Recovery processes are validated before incidents occur
- Snapshot and backup strategies are tested against real attack scenarios
- Storage infrastructure is configured to minimise recovery time
Expert’s Note:
“FlashSystem deployments are designed not just for performance, but for rapid recovery when organisations need it most.“
Technical Specifications
Deep-dive into the infrastructure capabilities for IT Managers and Architects.
NVMe Performance & Latency
Designed for fast response times, with ultra-low latency achievable in optimised environments.
Ideal for databases, virtualisation, and emerging AI workloads.
Safeguarded Copy & Cyber Resilience
Immutable, logically isolated snapshots help protect against ransomware and internal threats. Supports controlled recovery and validation for stronger cyber resilience.
VMware & Hybrid Cloud Integration
Seamless integration with VMware (VAAI, SRM) to simplify management and recovery. Enables data mobility across on-premises and cloud platforms, including IBM Cloud, AWS, and Azure.
Data Reduction & Efficiency
Hardware-accelerated compression and deduplication reduce storage footprint and costs. Typically delivers data reduction ratios of up to 2:1 or higher, depending on workload.
We ensure your response plan is not just compliant — it’s operationally sound.
Ready to elevate your storage strategy?
Modernise your storage with confidence. Whether you’re refreshing ageing infrastructure, addressing performance bottlenecks, or strengthening protection against ransomware, we’ll help you design an IBM FlashSystem solution aligned with your workloads, growth ambitions, and recovery objectives.
- Book your discovery session now